Contributors
Cyber technology was not invented in Israel. Forty years ago, various countries such as Russia, the United States, Britain (and Israel) used cyber technology for intelligence and security purposes. But Israel was the first country in the world to “come out of the closet”, that is, to make cyber technology a legitimate occupation for civilian industry, and to open it up to areas such as academic research, education, business, and other areas of normal life.
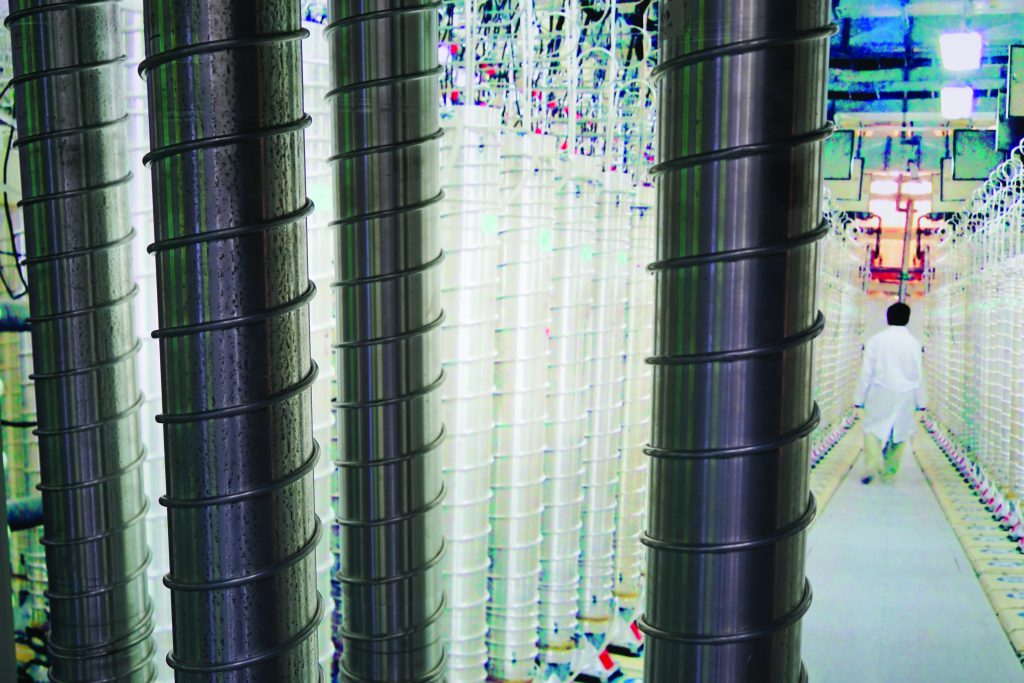
“Cyber threats” have become known to everyone in recent years. The term includes a wide range of phenomena such as: hacking into government computerized databases; stealing money through fake banking instructions; publishing credit card numbers; encrypting and “locking” sites as extortion and releasing them for ransom; vandalizing sites; shutting off and damaging power plants; hitting transportation systems (including sea and air traffic); damaging sensitive facilities (like the centrifuges at the Iranian uranium enrichment facility in Natanz); cross-border espionage and commercial espionage; the distribution of fake news through the internet and social networks in order to influence public opinion; and more, and more.
As strange as it may sound, about a decade ago the term “cyber” was known only to a very small number of people, especially those coming from defense and intelligence organizations. For example, a decade ago, there was not even a single university in the world where cyber security could be studied. So how did the revolution happen?
In the beginning there was intelligence
The mission of intelligence agencies is, of course, to gather information about security threats. To this end, the intelligence agencies have always dealt with espionage, eavesdropping on conversations, reconnaissance, and so on. The rapid development of computer technology led, in the early 1980s, to the replacement of telephone switchboards from mechanical switches to computer servers. At the same time, computer media has become the primary means of storing and processing information. The intelligence agencies were thus forced to find ways to hack into computers in order to continue their classic missions. Gradually, a new discipline, called information security – the protection of information stored in computers – also began to develop.
The rapid development of computer technology and especially computerized communication networks led to a change in the warfare doctrines of advanced armies (with the IDF among them). For the first time, it was possible to take information gathered in one place and pass it, almost without delay, to a fighter in another place.
The designers of Israel’s security doctrine understood that Israel, being the most computerized country in the Middle East, could be very vulnerable to cyber-attack. Therefore, at this time, over twenty years ago, we were the first country in the world to prepare itself, in effect, for a future cyber war
This is one of the reasons that led the US military in the early 1990s to formulate a new doctrine of warfare – Revolution in Military Affairs (RMA) – which was based on four pillars, one of them was “Information Warfare”. The intention was to disrupt, distort and prevent the use of information that our enemy needs for combat (along with securing of the information on our own side).
At the same time, the rapid miniaturization of computer chips has made it small enough to fit into any combat platform. Navigation and bombing computers were put on planes and took on some of the pilot’s missions, as well as on ships and in tanks. The further miniaturization brought computer chips inside the weapon itself, thus opening up the age of smart weapons. This development led some armies (including the IDF), as early as the 1990s, to explore the possibility of using cyber technology (which was already sufficiently developed for information-gathering purposes) as a weapon: neutralizing enemy aircraft, for example, can be done through kinetic damage (by anti-aircraft artillery or missiles), but also by disrupting their electronic operation (electronic warfare) or by disrupting computers on the planes if one succeeds to infect them with cyber viruses.
From information warfare to cyber warfare
It soon became clear that the ability to use cyber as a weapon, in the military arena, is not so simple, and it is actually easier to hit computers of civilian systems. This observation has led Israel’s defense security designers to understand that Israel, being the most computerized country in the Middle East, is potentially very vulnerable to such an attack. This understanding, driven by several people (including the author of these paper as the Head of the Defense R&D Directorate of IMOD), led the Israeli government in 2002, to establish a new body – the Information Security Authority – in order to oversee and protect critical infrastructure, such as power production facilities, water supply systems and the like. This is how Israel became the first country in the world (20 years ago) to be prepared for a future cyber war.
This was, in fact, the result of a deeper understanding than that which appears on the surface: it turned out that the dependence of critical systems on computerized controllers had grown to such an extent that disrupting controllers could cause real physical damage rather than just “virtual” damage to the information space. The era of information security was over, and the era of cyber security had begun.
The possibility of physical damage by cyber technology burst into global awareness following the collapse of centrifuges at Iran’s uranium enrichment facilities in 2010. It was the first time the wider world had been exposed to the possibility of inflicting physical damage by “virtual” cyber-attacks. Like a bolt of lightning on a sunny day, it suddenly became the subject for broad public discourse. Following this, I was appointed by the Prime Minister to head a multidisciplinary task force in order to prepare Israel for future cyber threats. The team examined the issue from a very broad perspective and asked the more general question: what needs to be done in order to build a living and sustainable ecosystem that will keep Israel continuously prepared against cyber-attacks in the future?
The plan submitted to the government was based on several basic assumptions.
The possibility of physical damage through cyber technology burst into our global awareness following the collapse of centrifuges at Iran’s uranium enrichment facilities in 2010. It was the first time the wider world was exposed to the possibility of inflicting physical damage by “virtual” cyber attacks
The first was that the pace of development of computer technology is so high (a new generation appears about every year) that it is impossible to predict and prepare for future threats.
The second was that cyber threats are the dark side of computer technology: as computers play an increasing role in our lives, so too will there be an increase in the number of new vulnerabilities and opportunities for cyber-attacks.
A third assumption was that since computers penetrate every area of our lives, the practice of cyber must be inherently multidisciplinary. Cyber solutions are usually technological, but the problems are almost never just technological. They cannot be solved without taking into account the psychology of the user, the behavior of the masses, creating trust from the users, the tension between conflicting values (like security and privacy), problems of law and regulation and more.
Therefore, the only solution is to build an entire ecosystem that will know how to quickly take care of new, unpredicted, emerging cyber threats, continuously. Such a solution must rely on knowledgeable people who will understand the situation, and a large supply of technologies, even if they are not mature, that will enable rapid implementation (in other words, directing start-ups towards cyber).
In 2011, I submitted the report to the Prime Minister. It contained a series of recommendations concerning not only technology but also subjects like capacity building; integration of industry, academia and security agencies; education in schools and universities; the establishment of centers of excellence in academia; resolving export issues; the establishment of necessary national infrastructures (such as supercomputers and simulators); ethics; regulation, etc.
In 2020, Israeli exports in the cyber sector amounted to 6.85 billion dollars, i.e. 5% -10% of the global civilian market. To this one can add 2.9 billion dollars in fundraising and about 20 major acquisitions worth over 4.7 billion dollar
The main idea was to create the following magic circle: (1) academia will create new knowledge; (2) industry will rely on this knowledge and develop advanced capabilities with high added-value in accordance with market needs and global demand; (3) the defense system will enjoy the new knowledge and capabilities and in turn will contribute excellent manpower, unique needs and understanding that will nourish academia and industry. Thus, (4) through the transition of talented people from the defense system to industry and academia, an intertwined system of tools will be created in which knowledge will pass extensively between these three systems (defense and government, industry and academia).
All of these became a government decision in November 2011 and the National Cyber Bureau was established in the Prime Minister’s Office. It should be emphasized that the mission defined for the Cyber Bureau was not the daily protection against attacks, but the supervision, planning and conducting of the buildup of the entire ecosystem.
In 2015, another tier was added to the system: the National Authority for the Protection of Civil Cyber Space (also on the recommendation of a team that I headed up on behalf of the Prime Minister). This was later merged with the cyber headquarters into one body called Israel National Cyber Directorate.

Army of Unicorns
Today, only ten years after the program was launched, Israel plays a central role in the cyber world. Israel is the only country in the world where cyber is a subject for the matriculation examination at the end of high school. The magic circle mentioned above created a strong cyber industry and the number of cyber companies, from the start-up level to unicorns (companies worth over $1 billion), is unprecedented.
The numbers speak for themselves. For example, in 2020, Israeli direct exports of defensive cyber security products amounted to $ 6.85 billion, i.e. 5% -10% of the global civilian cyber market. To this must be added $2.9 billion in fundraising and about 20 major acquisitions worth $ 4.7 billion. When looking at the global investments in the cyber business sector, it turns out that 31% of them were directed to Israel. In 2020, five Israeli cyber companies were added to the list of unicorn in the world, bringing the rate of Israeli unicorn companies to 33% of the total number in the world. In the first half of 2021, Israel’s share of global investments in the cyber business sector rose to 46%, placing Israel at the top of the list, ahead of the USA.
It is important to emphasize that all these steps, which seem natural and almost self-evident, have been done by a number of countries that can be counted on the fingers of one hand only. This is why the annual Cyber Week Conference at the Tel Aviv University campus, has become a center of pilgrimage from all over the world. In recent years it has been attended annually by almost 10,000 people who originate from over 90 countries. The conference will be held this year too, starting on July 19th, despite corona.
The next move
However, computing technology is not standing still. The day is not far off when we will make the next leap – to quantum computing technology – which will increase the performance of computers by a factor that is difficult to digest (10 to the power of 30). This is not the only expected development. The world of technology is heavily engaged with the design of a smart home, a smart city, the Internet of Things (IOT), and so on. The idea is simple: let’s turn every appliance in our lives (refrigerator, car, washing machine) into a computer-controlled appliance and tie all this stuff into a communication network that will be the ‘Internet of Things’. Some people are even bolder: they talk about a smart city and even a smart country. Moreover, the development in the field of learning algorithms brought artificial intelligence (AI) back to center stage and this began to be integrated into the overall vision.
All this will not be possible without a minimum level of security. If we do not take security breaches seriously, the ‘bad guys’ (and such will always exist) will be able to take advantage of all these developments for terrorism, crime and irreversible damage.
The future therefore requires a minimum level of security that will enable all these innovations. We are at the beginning of a time when cyber security is no longer an end-in-itself (i.e. securing everything that is computer-controlled). It is, in fact, an “enabler” technology, without which we will not be able to move in the desired direction.
Professor Isaac Ben Israel is a contributor head of Yuval Ne’eman Workshop for Science, Technology and Security, Director of the Blavatnik Interdisciplinary Cyber Research Center of Tel Aviv University and Chairman of Israel Space Agency.
Forbes Israel Contributors are independent writers that were individually picked by Forbes staff. The writers are experts in their field and they provide professional commentary and analysis of current events. The Contributor’s content isn’t sponsored.





