Most modern-day threat actors try to remain under the radar. They use different tools and techniques to infiltrate the targeted network, not trigger any alarm, map out the targeted infrastructure and steal data quietly and covertly. This is not the case when it comes to Ransomware. Once activated, Ransomware attacks are very visible and very disruptive, demanding large amounts of money for decryption of the data, and in some cases – additional payments for them to not publicly release the stolen data. The latest victim of such as attack is GPS tracker giant Garmin.

The sensitivity of this data has already been demonstrated several years ago when a researcher used Strava data to show where military personnel do their everyday workout. Combine that data with google maps and you can identify secret military bases.
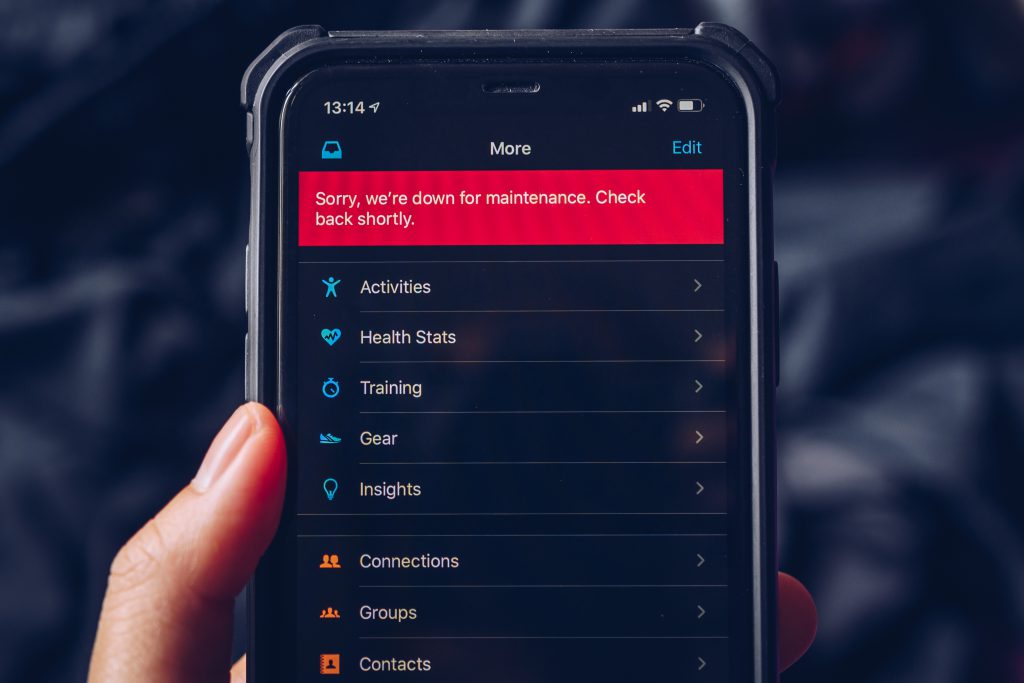
Using the WastedLocker Ransomware, the EvilCorp group (who is known for their attacks on financial institutions) successfully halted the operations of Garmin and demanded a $10M ransom. Users of Garmin’s products immediately noticed issues when trying to connect and sync their devices with Garmin’s servers, but sport and healthcare trackers were not the only ones experiencing difficulties. Pilots could not download maps into their FlyGarmin app (used by Garmin GPS based instruments), the Garmin Pilot app (used for scheduling and planning flights) was experiencing difficulties as did the Garmin watches used by air force fighter pilots.
There are multiple privacy issues when it comes to fitness trackers. While it is great to have a detailed log of our sporting activity and watch our progress over time – what we should be asking is where is this data stored? Who can access this? The sensitivity of this data has already been demonstrated several years ago when a researcher used Strava data to show where military personnel do their everyday workout. Combine that data with google maps and you can identify secret military bases. The problem, unfortunately, does not end with location data.
Today’s fitness trackers also allow users to enter additional medical data manually or integrate with other services and applications and share the data across multiple services. This raises multiple privacy and compliance issues on top of Personal Identifiable Information data leakage.
Dual payment
In recent months IntSights researchers have seen an increase in Ransomware “dual payment” attacks. These Ransomware attacks demand two payments, one for reversing the encryption and allowing the business to recover, and the second for them not to share the stolen data with the rest of the world. The silver lining in Garmin’s case is that EvilCorp has (at least so far) asked money only for realising the locked files. Other notable groups however, such as the Maze team, have not been so “kind”.
The attack on Garmin, which according the latest updates has been resolved (rumours are the $10M has been made) raises serious questions, not just on the personal privacy level but also for national security and operational readiness. Unfortunately, this is not the last we have seen of large-scale Ransomware attacks. Frank Abagnale (who’s story was the subject of Spielberg’s “Catch me if you can”) said in one of his talks “every breach happens because someone at the organization either did something they shouldn’t have or didn’t do something they should have” – eluding to people falling for phishing attacks in the former and to systems not being patched or properly secure in the latter.
No technology can bullet proof organizations from human error, and with more connected devices, sharing more information with more systems organizations and governments need to take a deeper dive into risk management, cyber threat intelligence and breach preparedness.
Etay Maor is Chief Security Officer at IntSights





